Using JXplorer to connect to vSphere PSC Server
JXplorer is a cross platform LDAP browser and editor. It is a standards compliant general purpose LDAP client that can be used to search, read and edit any standard LDAP directory, or any directory service with an LDAP or DSML interface.
Note: Please take extreme care when connecting to the vmdird database. This is not a recommended way of viewing this data but it can be very useful
JXplorer Download Location
I installed this on a Windows 10 workstation which had connectivity to my PSC Servers
Configuration Steps
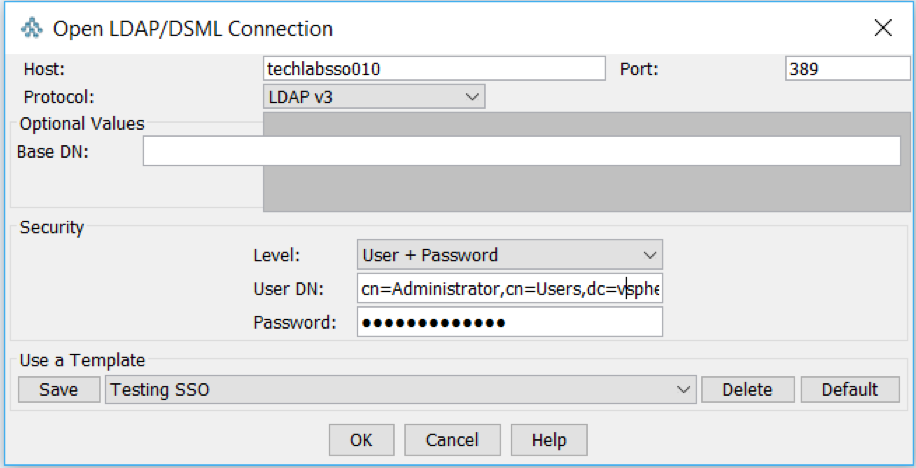
- Open JXplorer and open a new Connection
- In the Host field put in the same of your PSC/SSO Server
- Don’t put anything in Base DN. It will let you connect if you do put a Base DN in but will error when you try and expand the tree
- In Security Level, choose User + Password
- In User DN, type CN=Administrator,CN=Users,DC=vsphere,DC=local
- Put in your PSC/SSO password
- Save the template
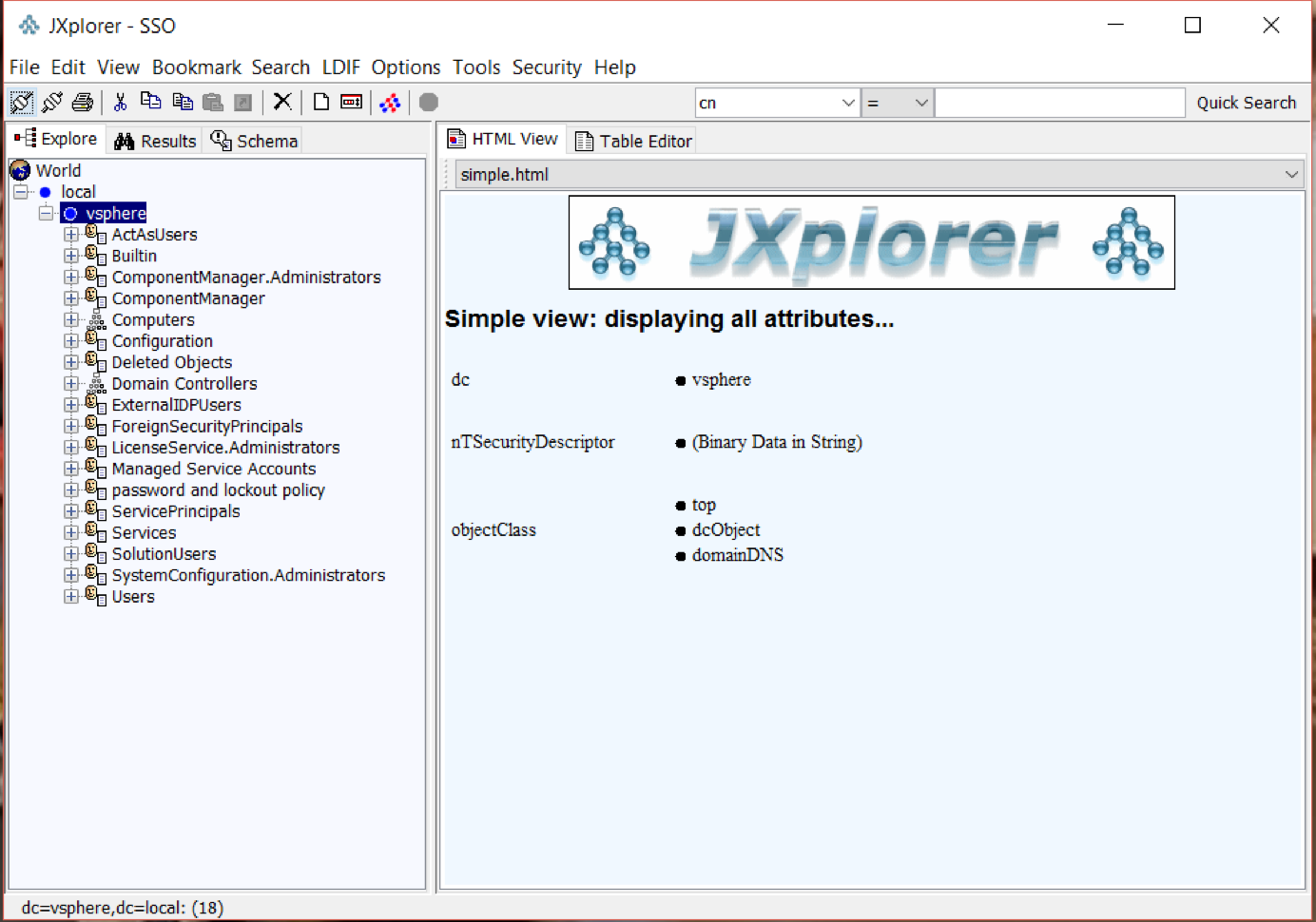
- You should now see the following screen
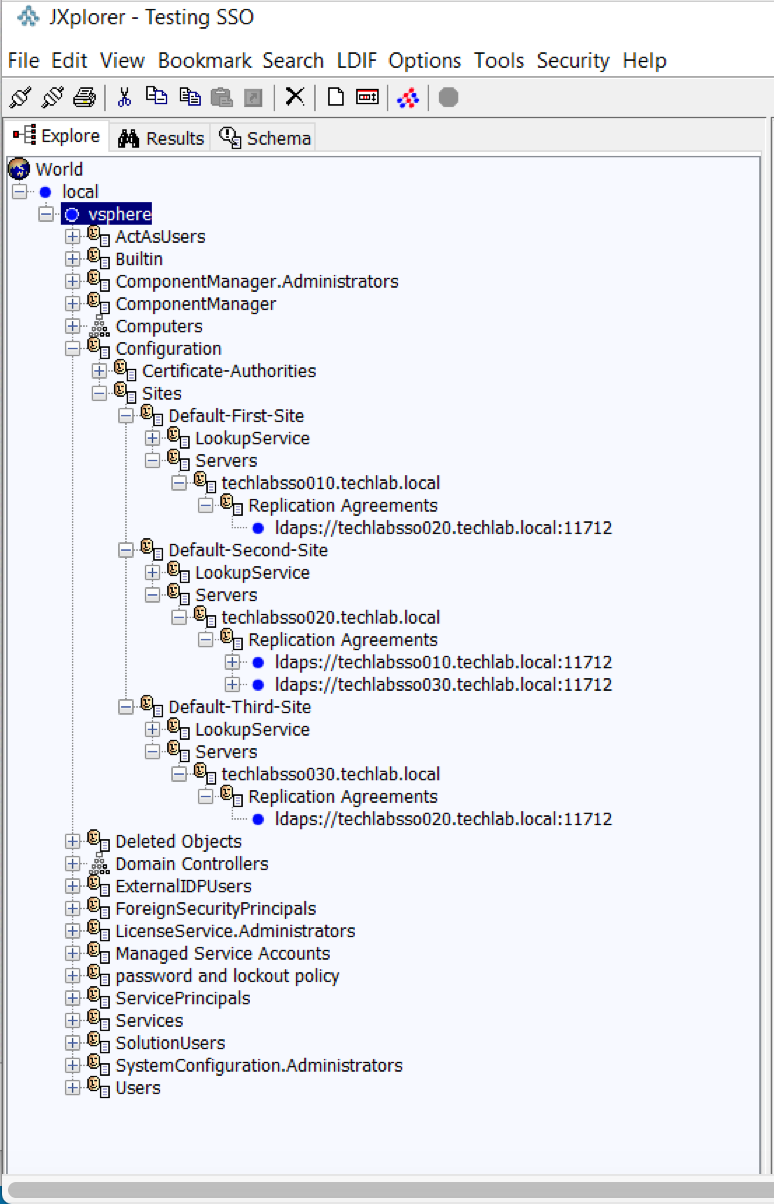
- Expand vSphere > Configuration > Sites and you should be able to see all the replication agreements.
- I’ve been playing around with multi-site scenarios which is why you can see Default-First-Site, Default-Second-Site and Default-Third-Site which are my 3 PSCs in a multisite scenario.
Other Observations
Information from Sung Rao (VMware) Thank Q
In 5.5. the only secure LDAP communication between SSO/PSC nodes are via LDAPS. Thus in automatic replication agreements establishment, LDAPS is used.
In 6.0 and after, we introduced LDAP SASL/SRP binding which go through port 389. LDAP SASL/SRP (or KRB) is the simple and safe to manage between LDAP nodes. This binding mechanism is preferable to LDAPS as the SSL port is difficult to manage/deploy correctly as it depends on PKI. Also, LDAP layer sites below certificate. You need an ID before you can get a cert
Regardless, in 6.0 and after, the server will try SASL/SRP first and fall back to LDAPS if necessary regardless of LDAP/LDAPS in the labeledURI in the replication agreement definition. You also cannot force the replication agreements to use LDAPS in 6.0 and after