How can we install software remotely from Group Policy?
- Assigning Software
You can assign a program distribution to users or computers. If you assign the program to a user, it is installed when the user logs on to the computer. When the user first runs the program, the installation is completed. If you assign the program to a computer, it is installed when the computer starts, and it is available to all users who log on to the computer. When a user first runs the program, the installation is completed. Assigned means that the application appears on the start menu.
- Publishing Software
You can publish a program distribution to users. When the user logs on to the computer, the published program is displayed in the Add or Remove Programs dialog box, and it can be installed from there
What type of software file can we deploy?
The Group Policy Management Console’s job is to deploy MSI files. GPMC can also deploy other kinds of files, but I’m going to skip over that for today and focus only on MSI files.
Remember: MSI files are application packages that come from manufacturers (or, you can also create them yourselves with 3rd party MSI repackaging tools.
Step 1 Create a Distribution Point
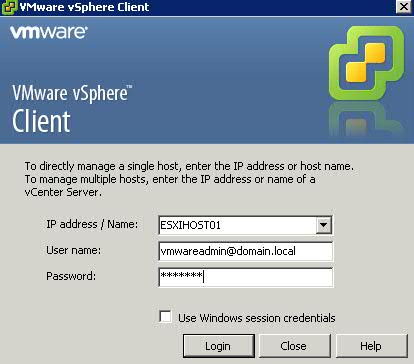
- Log on to the server as an administrator (I am using my Test Lab)
- Create a shared network folder where you will put the Microsoft Windows Installer package (.msi file) that you want to distribute
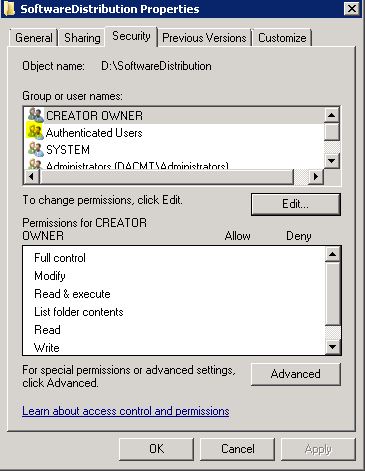
- Set permissions on the share to allow access to the distribution package.
- You must add Authenticated Users with Read Access to the Share and NTFS permissions if you are applying this to Computer OUs as Computers are Authenticated Users in AD
- Copy or install the package to the distribution point.
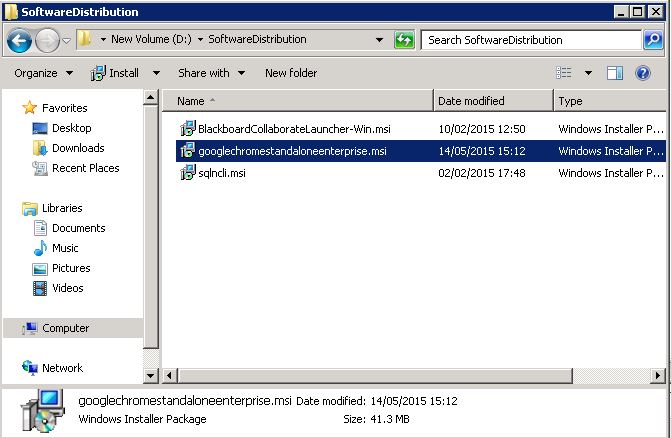
- I’m going to use the Google Chrome 32bit .msi
Step 2 Create a Group Policy Object
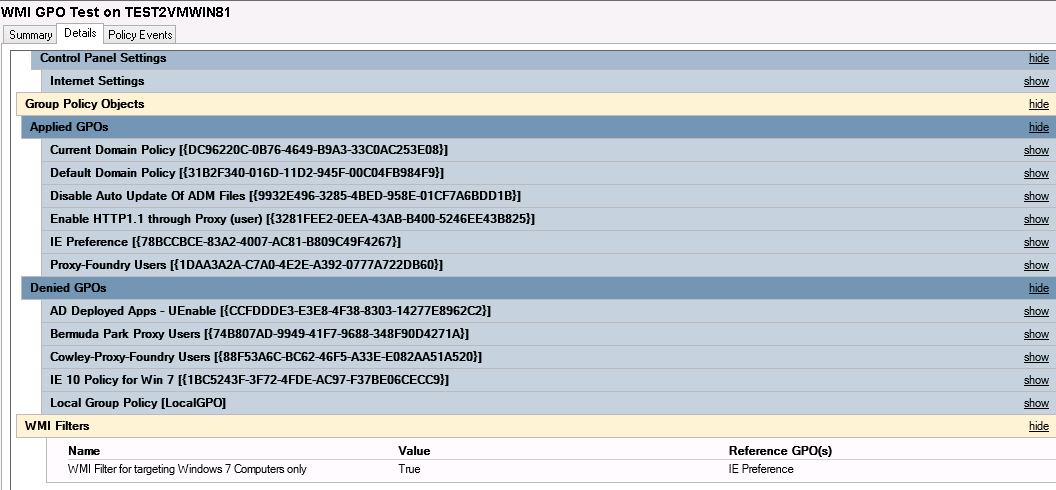
- I am just going to test this on a Windows 7 machine
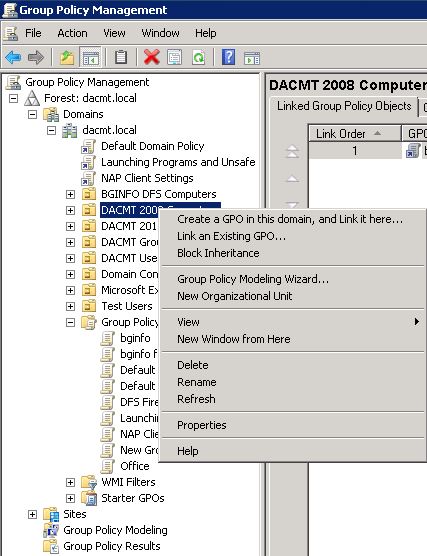
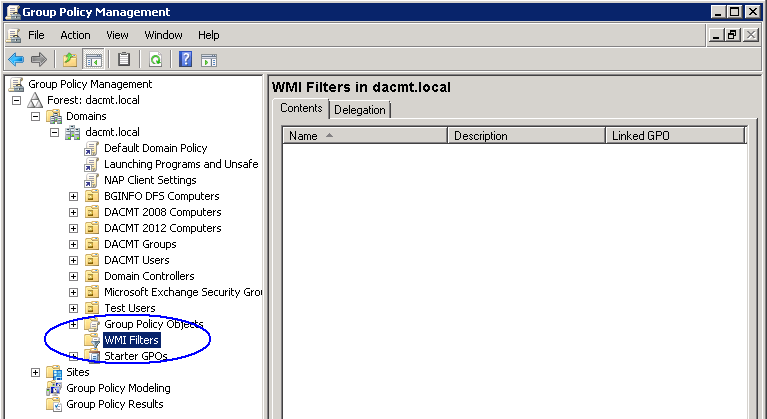
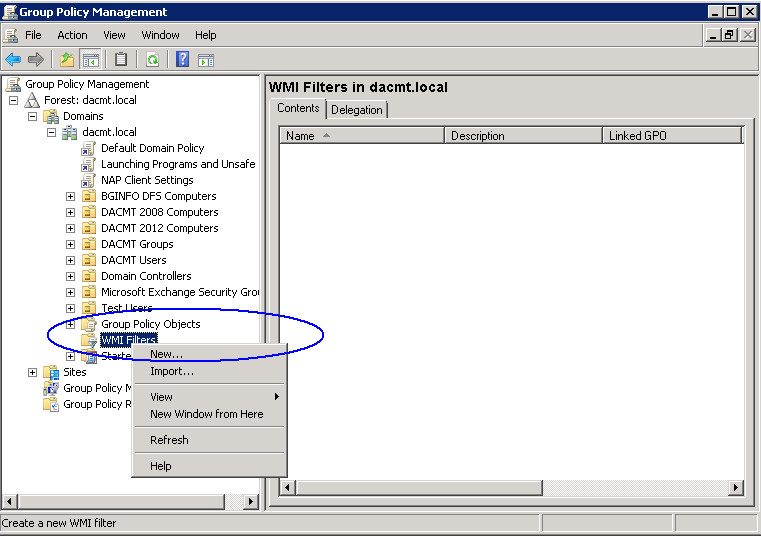
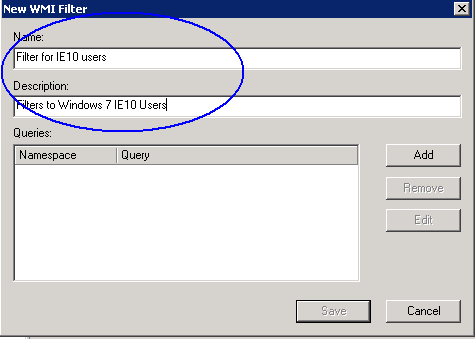
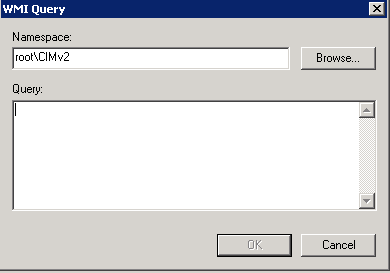
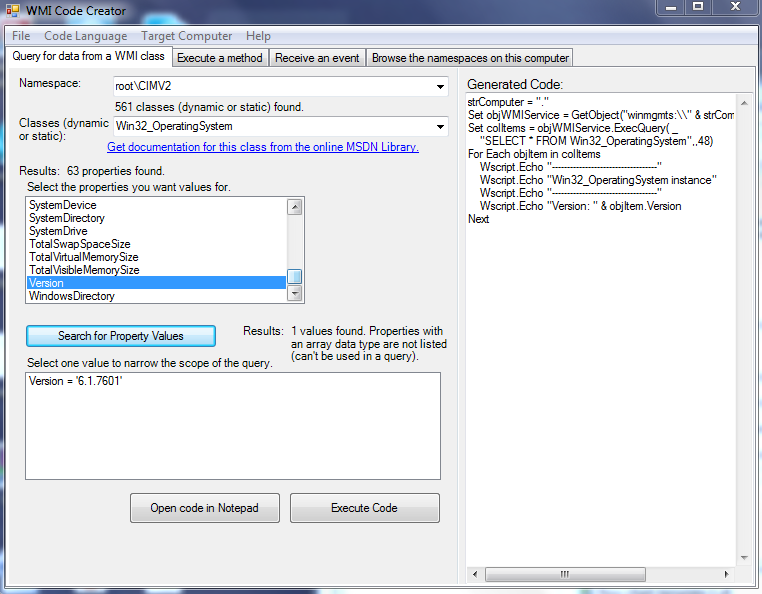
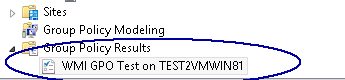
- Open Group Policy Management Console
- Find the OU which contains the computer/computers you want to apply the policy to and right click and select Create a GPO in this domain and link it here
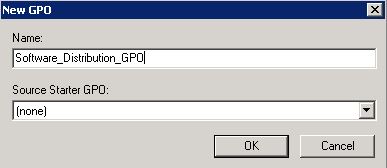
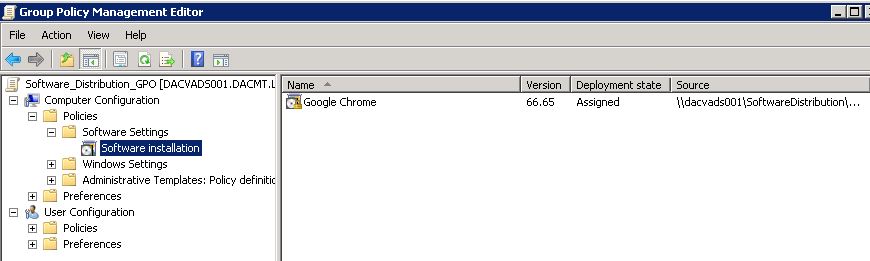
- Put in a name. Mine is Software_Distribution_GPO
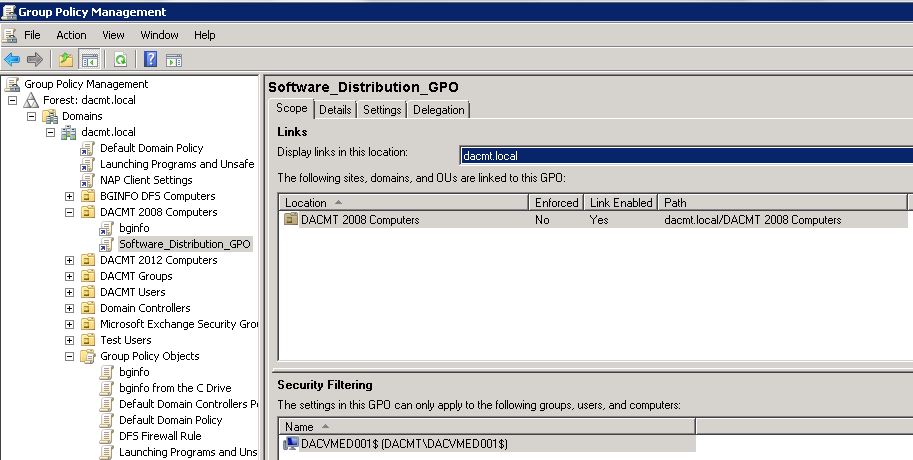
- Click on the policy and select it.
- In my policy I am going to set the security filtering to just my Windows 7 test machine (dacvmed001)
- Click Edit on your GPO
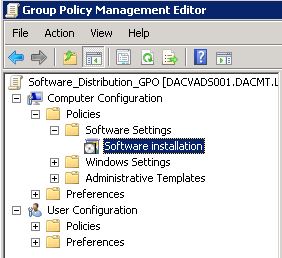
- Under Computer Configuration expand Policies to see Software Settings
- Right click and select New Package
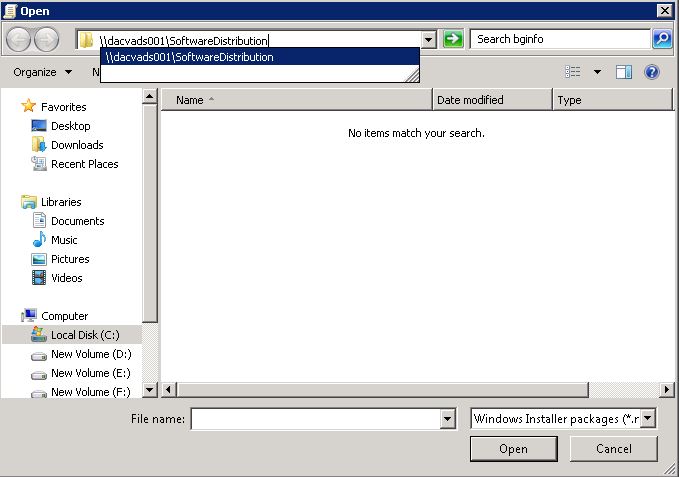
- Type in the full (UNC) path to your Software Distribution share. In my case \\dacvads001\SoftwareDistribution
- You should now see your .msi software
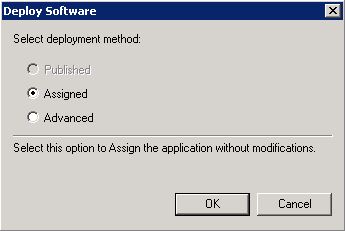
- Click Assigned. If you click Advanced, it gives you options to configure Published or Assigned Options and to apply modifications to a package
- NOTE: The Published option is greyed out as it is only available if I deploy my package to a User Container. Software deployed to computers does not support publishing
- You can now see your package in your GPO
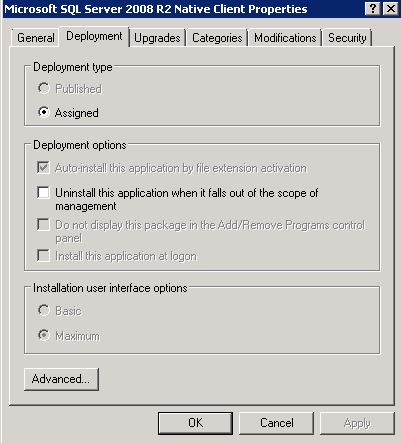
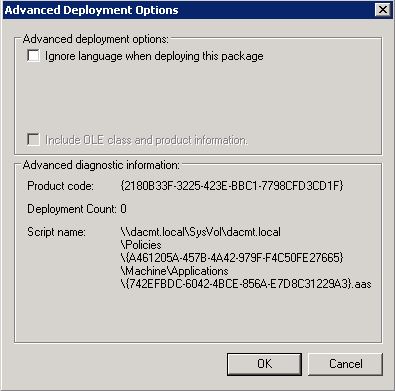
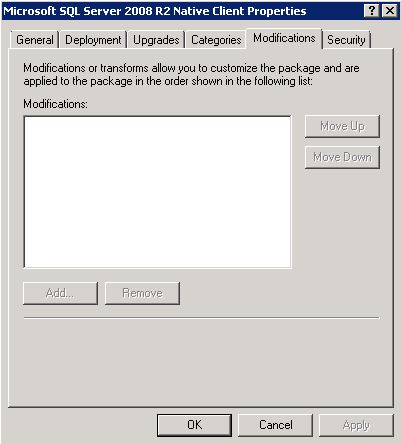
- If you right click on your package and select Properties, you can see further information. Note I have screenprinted the properties of the SQL Client
- The General Tab
- The Deployment tab
- Basic means that the user will see few / no screens when the application installs.
- Maximum means that the user will have full interaction when the application installs.
- Advanced Options
- Upgrades
- Categories
- Modifications
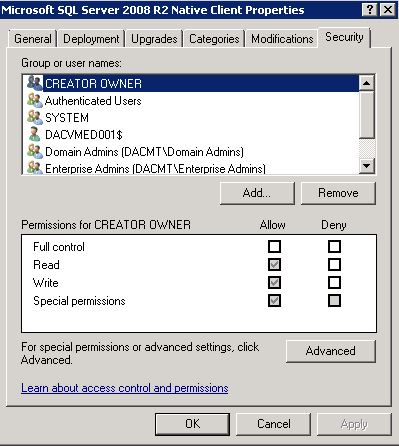
- Security
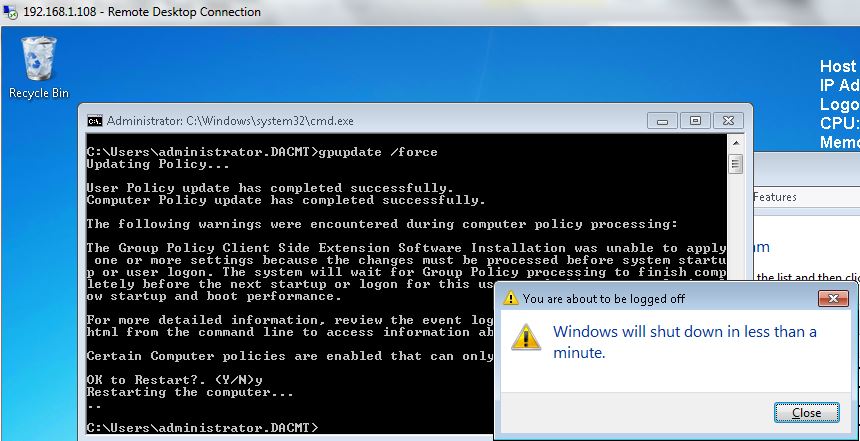
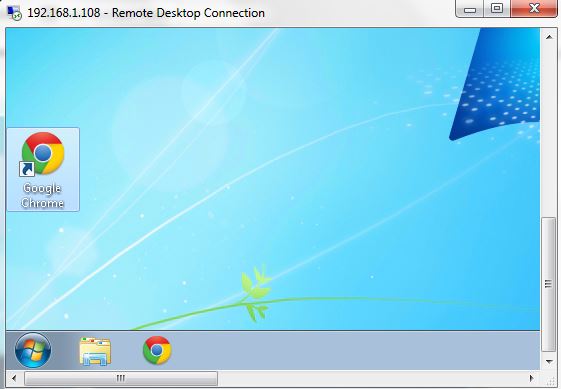
- Next do a gpupdate /force on the Domain Controller and reboot your PC.
- Check that the software has been installed in Control Panel > Programs and Features
Redeploy a MSI package
Sometimes you may need to redeploy a package (for example when doing an upgrade). For redeploying a package you can follow these steps:
- Open Group Policy tab, select the object you used to deploy the package and click Edit
- Expand the Software Settings element (per-user or per-machine) which contains the deployed package
- Expand the Software Installation element which contains the deployed package
- Right-click the package in the right pane of the Group Policy window
- Select the All Tasks menu and click Redeploy application
- Click the Yes button for reinstalling the application wherever it is installed
- Close the Group Policy snap-in, click OK and exit the Active Directory Users and Computers snap-in
Remove an MSI package
Group Policy also allows you to remove packages which have been deployed in the past. Here are the steps for removing a package:
- Open Group Policy, select the object you used to deploy the package and click Edit
- Expand the Software Settings element (per-user or per-machine) which contains the deployed package
- Expand the Software Installation element which contains the deployed package
- Right-click the package in the right pane of the Group Policy window
- Select the All Tasks menu and click Remove
- Select from the following options:
- Immediately uninstall the software from users and computers
- Allow users to continue to use the software but prevent new installations
- Click the OK button to continue
- Close the Group Policy snap-in, click OK and exit the Active Directory Users and Computers snap-in
What can we do about .exe’s that we want to turn into usable .msi’s?
You will need to get a packaging utility to turn that .exe file into .msi file. Many of them are available for instant download from internet
One of the best one’s I have trialled is http://www.exetomsi.com/
Tips and Advice on EXE to MSI Repackaging